The discussion centers on whether a Phone Verification Insight Portal can reliably determine if a number is legitimate by explaining caller validation. It assesses how verification signals are gathered, weighed, and presented to users as trust indicators. The analysis notes the role of provenance, data sources, and transparent workflows in reducing uncertainty. Yet, it leaves unresolved how portals handle conflicting signals or evolving scam tactics, inviting further scrutiny of their methods and safeguards.
What Is Caller Verification and Why It Matters
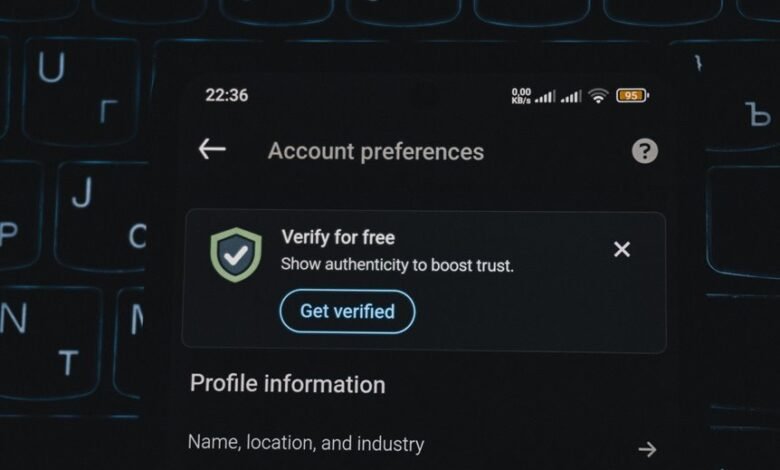
Caller verification is a process by which a system confirms that a phone number and the associated caller identity are legitimate before granting access or displaying trust signals.
This analysis frames caller verification as a control mechanism for autonomy, reducing uncertainty.
It highlights volt verification as a metric, notes scam indicators, and insists on robust data sources to deliver legitimate signals, enabling informed choice.
Signs a Number Is Legitimate: How Verification Signals Sleep On Your Screen
Determining legitimacy hinges on converging verification signals that appear on a device screen. The analysis remains detached, noting that caller validation emerges when multiple verification signals align: identity, provenance, and context. Subtle inconsistencies trigger scrutiny, while consistent indicators reinforce trust. Verification signals guide perception; legitimate numbers exhibit coherence, transparency, and verifiable metadata, reducing risk of deception for audiences seeking freedom and informed choice.
Spotting Red Flags: Common Scams and How Portals Validate Them
Spotting red flags in common scams requires a structured approach to pattern recognition, where abrupt requests for unfamiliar personal data, unsolicited offers, and pressure tactics are flagged as high-risk indicators.
The portal assesses Caller validation against Scam indicators, prioritizing Privacy safeguards and Verification signals.
Analysts note Caller ID tricks while ensuring Data protection through rigorous authentication and transparent, auditable verification workflows.
Practical Steps to Protect Your Info When Verifying Calls
Practical steps to protect personal information during call verification require a disciplined, methodical approach that minimizes exposure while ensuring legitimate validation. The analysis emphasizes minimizing data sharing, confirming requester identity through known channels, and avoiding unsolicited prompts. Clear privacy safeguards and verification best practices guide process design, user education, and incident response, ensuring control over data while sustaining legitimate verification goals.
Conclusion
In essence, the portal functions as an arbiter of trust, weighing signals much like a seasoned auditor assesses provenance and context. It mirrors the mythic trials of Odysseus, where hidden dangers are met with revelation and discipline. By foregrounding transparency, auditable workflows, and user-centric safeguards, it converts uncertainty into measurable assurance. The result is a disciplined framework: verify, scrutinize, and minimize data exposure, lest the voyage toward legitimacy yield deceptive shores.